What is Digital Forensics?
Digital forensics plays a crucial role in solving a large number of criminal and legal issues, both in the digital and physical world. This is owing to the large amounts of data captured by these devices from cars, mobile phones, routers, computers, and many others. Digital forensics has become a specialized area of forensics science owing to the collection, analysis, and preservation of electronic data to investigate and prevent cyber crimes. Some of the common spheres where digital forensics can be used are:
- Understanding the data breach and its attackers.
- Impact of the breach on the organization and its customers.
- Capturing violent crimes like assault, burglary, and murder.
- White-collar crimes like corporate fraud, extortion, and embezzlement.
- Identifying cybersecurity and physical security incidents.
Common Digital Risks
With a rapid increase in the number of interconnected supply chains, customers, and software vendors, it is common for organizations to expose their assets to digital attacks. They also tend to create multiple new attack surfaces by leveraging complex IT environments such as on-premise and mobile endpoints, and cloud-native technologies.
Branches of Digital Forensics
Computer Forensics-
This involves identifying and analyzing digital data to identify, preserve, recover, and analyze facts on the inspected information.
Mobile Device Forensics-
This involves investigating any device with internal memory and communication functionality such as mobile phones and tablets.
Network Forensics-
It is a proactive investigation process that involves monitoring, registering, and analyzing network activities.
Forensic Data Analysis (FDA)
This process focuses on analyzing structured data that is present in different application systems and databases related to some financial crime.
Database Forensics
These forensics help in identifying fraud in database transactions. It involves access to multiple databases and reporting changes made to that data.
Process of Digital Forensics
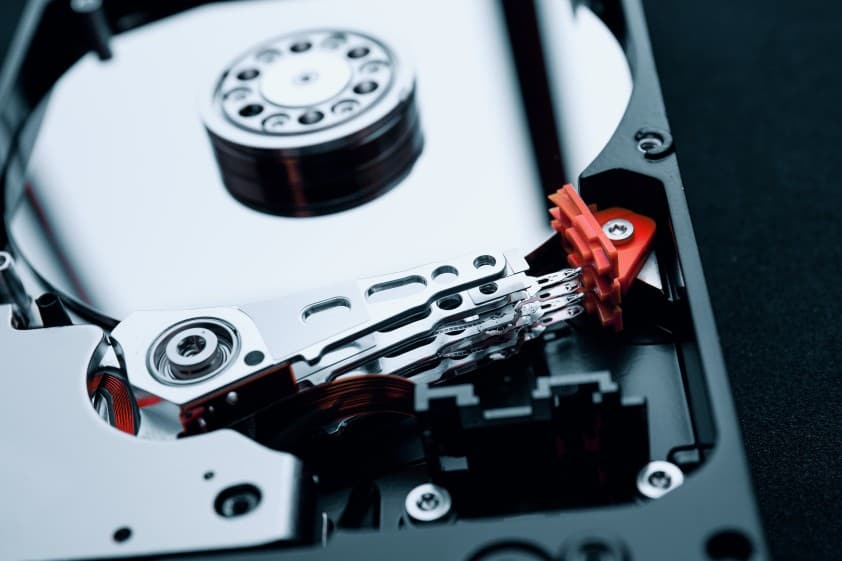
Collection-
This is the primary and most crucial step in digital forensics. This is because it involves data collection from multiple sources, which is usually done by seizing physical assets like mobile phones and computers. The best way to prevent data loss during this step is by copying the storage media or creating images of the original data.
Examination-
This step involves preparing, extracting, and identification of the collected data. The user can decide whether to work on the live or dread system when preparing to extract data. This can, then, be followed up by the investigation process wherein the user decides the parts of data relevant to the investigation.
Analysis-
This step involves finding answers to various questions such as who created and edited the data, how the data was created, when it was created, etc. The examiner also determines how the information is related to the existing case.
Reporting-
The reports are prepared based on the analysis conducted. The aim behind these reports is to ensure that they make sense to the common masses.